What is impersonation? And how to prevent?

Impersonation is the act of misleading someone by posing as another person for the purpose of fraud or entertainment which has evolved to become a dangerous form of cyberattack in the context of social engineering and cyber security. Through the act of impersonation, cyber criminals impersonate others to gain access to networks and system to commit fraud and identity theft to sell data on the dark web.
There are various methods of impersonation that criminals use, such as pretexters," which they employ to trick their victims and gain access to sensitive information. Pretexting is a form of social engineering where the attacker convinces a victim to give up valuable information or access to private data. A good example is an attacker pretending to be the CEO of an information technology company to collect information. Throughout their careers, impersonators can play many roles, such as those of fellow employees, technicians, IT support, auditors, and managers. The impersonator would need to carefully carry out research about the target for the attack to be successful. The attacks often take many forms and can target both individuals and businesses.
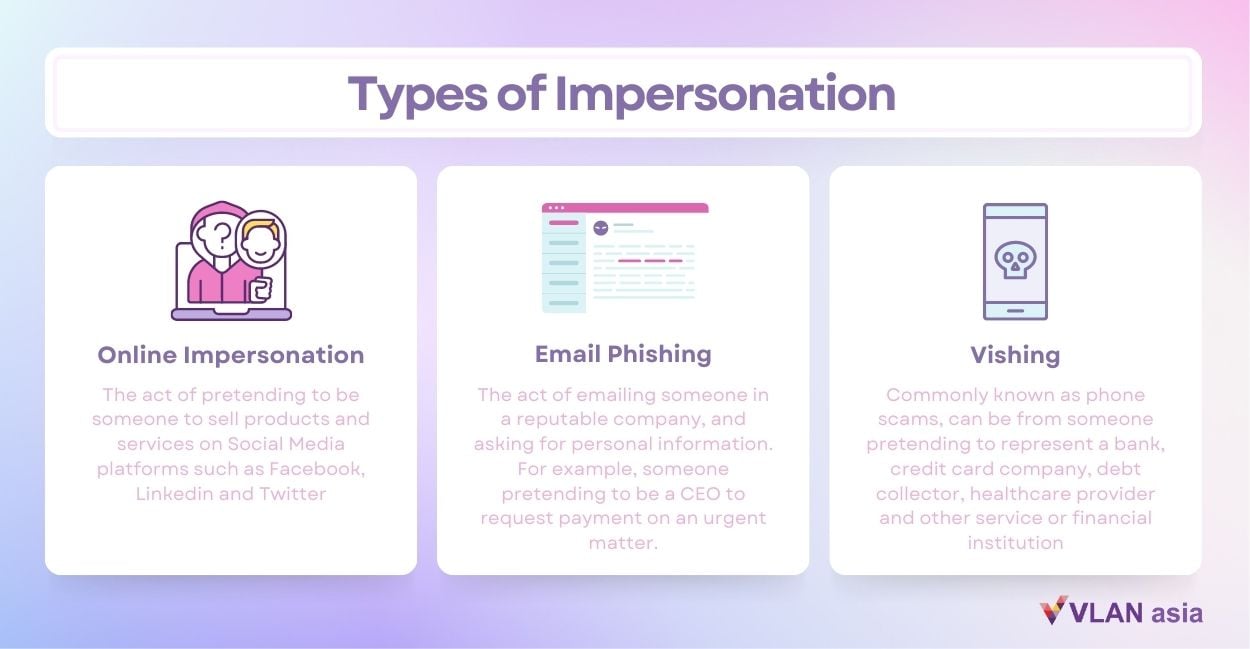
Types of Impersonation
Online Impersonation
Online impersonation is not automatically considered a criminal offence. For instance, nine out of the 50 states in the United States have laws addressing online impersonation, despite the fact that there are currently no federal laws on the matter. In Texas, using someone else's name, online identity, or persona to commit fraud, harassment, intimidation, or threatening behaviour can be punished by a hefty fine, a prohibition on accessing Internet-enabled devices, or even prison.
Online impersonation does not necessarily lead to fraud. Victims can experience defamation or extreme embarrassment. More and more social media platforms see impersonation as a violation of their terms of service and policy. According to Twitter”s impersonation policy, “accounts that pose as another person, brand, or organization in a confusing or deceptive manner may be permanently suspended.” Facebook says it does not condone this type of behavior in the community and encourages users to report a profile or page that does not comply with its policy.
Email impersonation and vishing (voice phishing)
The act of sending phony emails that appear to come from a reputable source to gain personal information is known as email phishing. To convince recipients that the message is real, attackers can impersonate well-known institutions (public or private) or individuals such as a co-worker or bosses.
Companies are a more profitable target for impersonation emails, in crimes such as business email compromise (BEC), CEO fraud, and whaling attacks. Attackers use emails carefully tailored to look like they come from business owners, executives, or human resources personnel, asking their target to carry out money transfers, pay invoices, or send important data.
In most cases, criminals rely on spoofing the email address and display name. The attacker chooses the name of a high-ranking individual from a business and sets up an email that looks similar to the victim”s. Impersonators can use publicly available information such as a name from LinkedIn to target people in an organization.
Commonly known as phone scams, vishing is also a popular attack vector among impersonators. The phone call can be from someone pretending to represent a bank, credit card company, debt collector, healthcare provider and pretty much any other service or financial institution.
[Other types of pretexting scams - summarised versions of all pretexting scams]
3 Ways to protect yourself against impersonation attacks

1. Train Your Employees
According to an article, 95% of security breaches tend to come from human errors. Thus, training employees effectively can assist to prevent cyber attacks from occurring.
Establish a dedicated cybersecurity manual and regular training sessions to educate staff members on the best safety practices they should adhere to. This can include advice on how to never sign in from a public device and how to periodically change account passwords.
It is also important to encourage employees to identify any urgent emails about any senstive information (such as bank payments) received out of the blue. At the same time, employees should reach out to the tech team immediately should there be any breaches.
2. Social Media Monitoring
To avoid social media impersonation, consistently monitor social media platforms. To make sure no one is using your brand name to damage your reputation or deceive your clients, you should also keep an eye on branded keyboards and other general keyboards linked to your business, including misspellings and alphanumeric combinations.
3. Protect Your Company's Domain
One of the simplest and most frequent methods to mimic a company is by infringing on its website. If you don't take any proactive measures to stop domain spoofing, scammers can deceive your clients by setting up a phony online store in your company's name and eroding your sales.
Adopt a domain management solution that can automatically identify registered domains that are identical to yours across different platforms and recover them in order to safeguard your domain, stop spoofing, and maybe stop company impersonation.
To find out more on how to safeguard your organisation, contact our sales@vlan.asia to know more about our solution.